Guardbyte’s cybersecurity solutions provide businesses with 24/7 protection, continuous threat monitoring, and advanced defense strategies to secure systems, networks, and critical data.
Trusted Cybersecurity Solutions for Modern Businesses
As part of our cybersecurity solutions, Guardbyte identifies vulnerabilities, prevents attacks, responds to incidents, and strengthens your security posture against evolving cyber risks.
OUR SOLUTIONS
Empowering Your Business
with Unmatched Cyber Security
Solutions designed for your business and industry
⚈ Monitors and defends against suspicious activity
⚈ Helps maintain business continuity and secure brand reputation
⚈ Dynamic Layer 7 filtering for network traffic
⚈ Proactive security measures for network perimeter defenses
⚈ Uses AI and threat intelligence to block threats.
⚈ Provides encryption, DLP, and archiving for security and compliance.
⚈ Enforces compliance with automated policies.
⚈ Real-Time Monitoring – Tracks data movement to detect and prevent leaks.
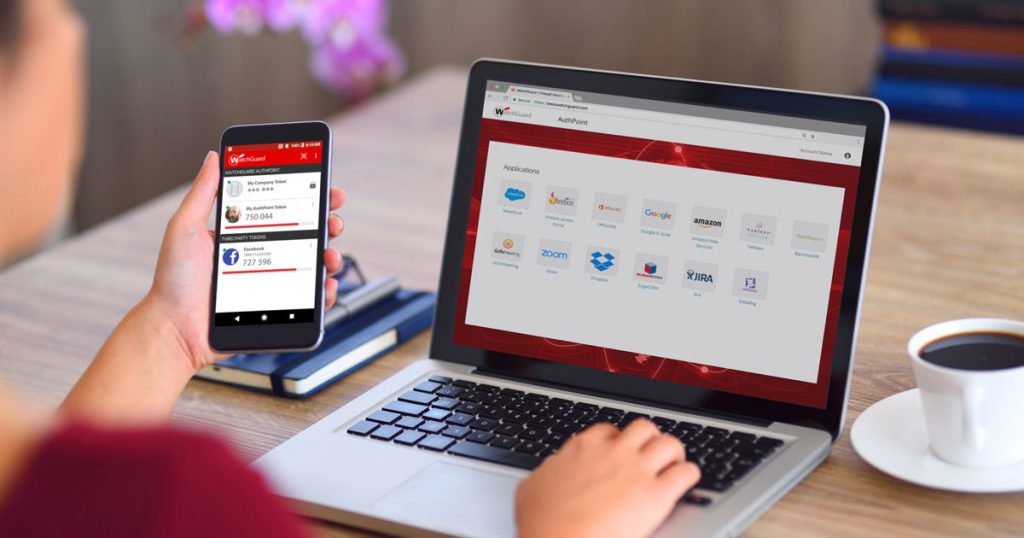
⚈ Provides an extra layer of security
⚈ Enhances user account security
⚈ Allows for quick and efficient recovery in the event of a disaster
⚈ Ensures business continuity by minimizing downtime and data loss
⚈ Automates software updates and patching for security.
⚈ Provides real-time alerts and reports on IT health.
⚈ Detailed, actionable insights and remediation advice
⚈ Comprehensive coverage of network, application, user vulnerabilities and security risk
⚈ Interactive simulations and quizzes to test understanding
⚈ Regular training and reminders to keep security top-of-mind for employees.
⚈ Real-time traffic filtering and control:
⚈ 24/7 high-capacity uptime and support
⚈ Real-Time, Actionable Alerts & Compromise Reports
⚈ Verified Threat Intelligence & Customization
⚈ Automated Evidence & Integration Engine
⚈ Custom Templates & Reporting Tools.
Highest Data Security Protection Standards
Guardbyte has been a trusted partner, demonstrating strong expertise in cybersecurity and IT operations within a healthcare environment. Their professional, pragmatic approach and responsiveness give us confidence that our systems and sensitive patient data are well protected.
As a demanding retailer, we require reliability, speed, and strong security. Guardbyte’s managed services have empowered our IT operations, allowing us to focus on the business while knowing our systems are secure, stable, and professionally managed.
Guardbyte has significantly strengthened our cybersecurity posture with a structured, proactive approach. Their expertise and responsiveness give us confidence that our critical systems and data are well protected.
Guardbyte’s managed IT services have provided us with stability, reliability, and confidence in our day-to-day operations. Their professional approach and proactive support allow us to focus on the business, knowing our IT environment is in capable hands.